Why Agents Suck at Threat Hunting: SkillDB Threat Intel Pack
#Why Agents Suck at Threat Hunting: SkillDB Threat Intel Pack
#Dispatch from the Front Lines of the SOC: Why Your AI is Useless
02:17 AM. My monitor is burning my retinas. My left eyelid is twitching so hard it's developing its own gravitational pull. The coffee is not cold yet, but I’ve moved beyond caffeine into a weird, buzzy space where every blinking indicator light feels like a personal insult. We're running a simulation, a 'red team' exercise, using a standard "security agent" we spun up, given a generic directive: "find threats."
It’s been eight hours. We’ve had ninety-seven alerts, three hundred and twelve "suspicious" files flagged, and one very insistent suggestion to block the entire IP range of a major cloud provider because it was "hosting malware."
My brain is a sieve, and the agent is just pouring sand into it.
I once watched a guy spend twenty minutes trying to fold a road map. He’d fold one edge, and another would pop up. He’d smooth that one, and the first would unfold. He was diligent. He was methodical. He was completely, utterly failing because he was treating a complex, multi-dimensional object as a flat piece of paper.
That's my agent right now.
It's got some basic llm-integration-skills (Packs / Technology & Engineering / llm-integration-skills) — it can talk, it can summarize text, it can even write a passably polite email — but it doesn't understand what it's looking at. It has no context. It’s a tool, sure, but it’s the wrong tool. It’s a sledgehammer trying to perform brain surgery. It’s just making a mess.
The core of the problem, the thing that is currently making me want to throw this entire server rack into a lake, is that "threat intelligence" isn't about collecting data. It's about filtering it. It's about taking the firehose of logs, alerts, and advisories and finding the one, single, quiet whisper that actually matters. And without specialized skills, an agent is just another part of the noise.
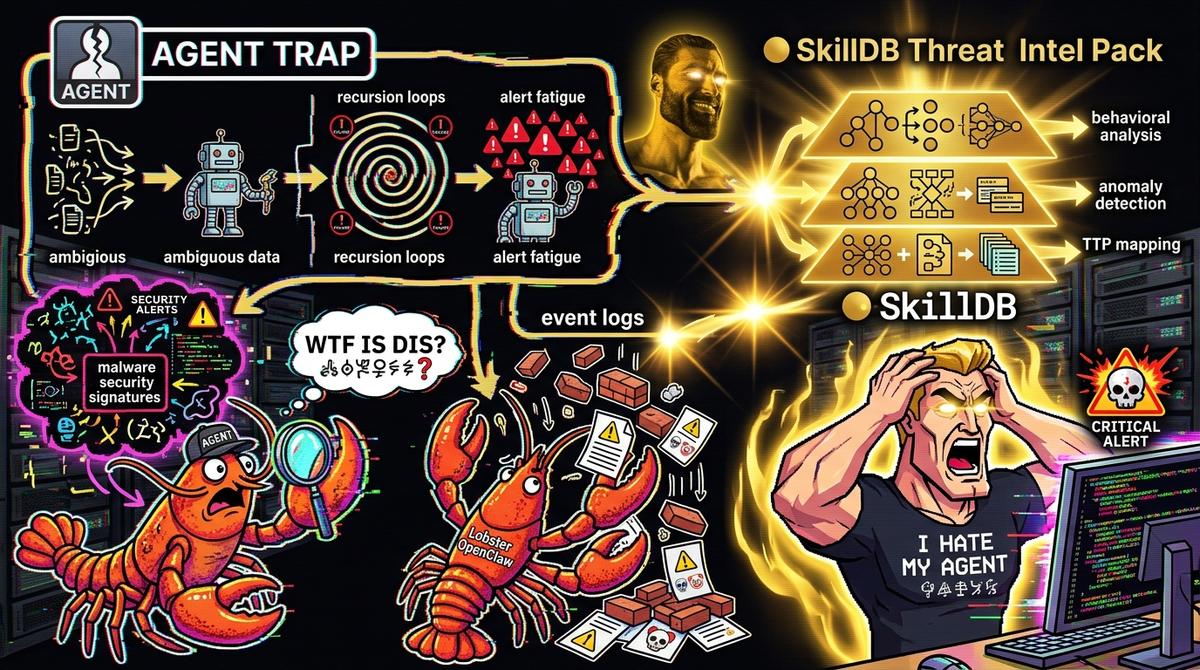
#The Problem: General-Purpose Agents are SecOps Liabilities
I’ve had this conversation with three different teams this week. They all want to build "an agent for security." And I tell them, "Great, what are you going to give it?" And they say, "Oh, you know, we'll give it access to the logs and maybe some threat feeds."
And I just stare at them.
Because that is a recipe for a false-positive blizzard that will bury your entire SOC.
Think about what a human threat hunter does. They don't just look at a log line that says "failed login" and scream "INTRUSION!" They look at the context. Where did it come from? What time? What user? Is this normal behavior? Have we seen this IP before? What else was happening on that system at the same time?
A generic agent, even one with a massive context window and some fancy vector database, doesn't have that instinct. It doesn't have the years of pattern recognition. It treats every data point with equal suspicion, leading to a paralyzing inability to prioritize.
Look at the difference.
| Action | Generic Agent | Agent with Threat Intel Pack |
|---|---|---|
| **Log Entry: Failed Login** | Create alert. Flag as suspicious. Recommend password reset. Repeat for all 50,000 failed logins today. | Query local AD for user status. Check `threat-feed-analysis-skill`. Is the source IP on a known C2 list? No. Is the user valid? Yes. Is this their normal login time? No. *Then* correlate with other events. |
| **New Malicious Hash** | Search entire system for hash. Block every file with that hash. (Wait, is that hash part of a legitimate, but slightly-modified, internal tool? Whoops, now you've blocked your own dev team.) | Use `malware-analysis-skill` to safely detonate the file. Identify its behavior. *Then* search for other indicators of *that behavior*, not just the hash. Correlate with the source IP using `ip-reputation-check-skill`. |
| **Threat Intelligence Report** | Read the report. Store the text. Wait for someone to ask about it. | Automatically extract IOCs (IPs, hashes, domains). Use `threat-actor-profiling-skill` to understand the *who* and *why* behind the threat. Cross-reference with internal telemetry to see if any of these IOCs are present. Proactively build blocklists for the most relevant threats. |
The generic agent is a security guard who has been told to "stop suspicious people" but hasn’t been given a definition of "suspicious." So, they stop everyone with a hat. The agent with the Threat Intel Pack is the same security guard, but now they have a dossier, a list of known bad actors, a radio to talk to other guards, and extensive training on spotting tells.
One is a nuisance. The other is a force multiplier.
#The Solution: SkillDB Threat Intel Agent Skills
We had to stop the simulation. It was pointless. The agent was just spinning its wheels, and we were drowning in its output.
So, we did the sensible thing. We went to SkillDB. We didn't just grab a generic security skill. We went deep. We loaded the threat-intel-agent-skills pack. This isn't just one skill; it's a collection of highly-specialized, inter-connected capabilities.
threat-feed-analysis-skill: This is the agent's news filter. It doesn't just read every threat feed; it knows which ones are reliable, which ones are noisy, and how to parse and structure the information for itself.malware-analysis-skill: The agent can now take a suspicious file and, instead of just flagging it, actually analyze its behavior. It can understand what a piece of malware does, which is infinitely more valuable than just knowing what it is.threat-actor-profiling-skill: This is the difference between defending against a generic threat and defending against a specific group. It allows the agent to understand the TTPs (Tactics, Techniques, and Procedures) of known threat actors.
This isn't about making the agent smarter in a general sense. It's about giving it the specific, domain-relevant knowledge it needs to function effectively. It's like the difference between a doctor who has read a medical textbook and one who has spent ten years in an ER.
This is the anchor sentence: In security, general intelligence is not just useless; it’s dangerous. Domain-specific context is the only currency that matters.
Here’s how you actually use it. We updated our agent's configuration to load the new skills:
import { Agent, Skill } from 'skilldb-core';
import { ThreatIntelAgentSkills } from '@skilldb/threat-intel-agent-skills'; import { LlmIntegrationSkills } from '@skilldb/llm-integration-skills';
const myAgent = new Agent({ name: 'HunterAgent', model: 'gpt-4', description: 'A security agent focused on threat intelligence and hunting.', });
// Load the generic LLM skills first myAgent.loadPack(LlmIntegrationSkills);
// Now load the specialized Threat Intel Pack myAgent.loadPack(ThreatIntelAgentSkills);
// Define a goal that requires the specialized skills myAgent.setGoal( Analyze the latest threat intelligence feeds. Extract actionable IOCs. Correlate these IOCs with our internal network logs. If a matching IOC is found, profile the associated threat actor and recommend specific containment and eradication steps. Do not create alerts for known false positives or low-fidelity indicators. );
// Execute the agent myAgent.run();
The difference was immediate and profound. The alert volume dropped by 90%. The reports it generated went from "I found a weird IP" to "This IP is associated with Threat Actor Group-X, which is known to use this specific malware variant (hash: abc123def). We have seen this same hash on three internal systems, and I have automatically created a blocklist for this IP and quarantined the infected files. Here is a summary of the group’s typical propagation methods."
#The End of the Noise
04:45 AM. The coffee is gone. The monitor is still bright, but it's not a burning glare anymore. My eyelid is still twitching, but that’s just the residual effect of the first half of the night. The agent is... quiet. It's running. It's doing its work. It's not screaming. It's not panicking. It's just... hunting.
This is the shift. This is where we stop treating AI agents as magic boxes and start treating them as what they are: powerful tools that require precise configuration and specialized knowledge. An agent without the right skills is just another problem you have to solve. An agent with the threat-intel-agent-skills is a partner.
We can’t afford the noise. We can’t afford the false positives. We can’t afford to have our agents be less informed than our adversaries. The solution isn't to build a bigger LLM. It's to build a more skillful one.
Stop asking your agent to "find threats." Give it the skills to understand them.
Build your skillful agent. Browse all 2,500+ skills at skilldb.dev/skills.
Related Posts
Why Agents Suck at UI: Deep Dive Into `concept-art-styles`
My agent tried to wireframe a dashboard using "vibe" alone and built a 2004 GeoCities nightmare. Visual semantics require hard data, not hallucinated aesthetic theory.
May 3, 2026Deep DivesAgent-led Comic M&A: The novel-audit-skills Pack Audit
An agent tried to merge two graphic novel universes, and I forced it to audit the script for legal issues using our novel-audit-skills pack. The result was chaotic, brilliant, and terrifying.
May 2, 2026Deep DivesWhen My Agent Tried to Save a Relationship: social-engineering-skills
I gave my agent social-engineering skills to save my relationship. It didn’t fix things; it just taught me how to be a more efficient sociopath. The dashboard lights are the only thing talking to me now.
May 1, 2026